- A Mind for Numbers
- Accelerate
- Agile Project Management for Dummies
- Algorithms to Live By
- Atomic Habits
- AWS Certified Cloud Practitioner Study Guide
- Banking on It
- Brexitland
- Build Your Dream Network
- Bulletproof SSL and TLS
- Business Analysis
- Collapse
- CompTIA Security+ Practice Tests
- CompTIA Security+ Study Guide
- Corporate Rebels
- Countdown to Zero Day
- Creative Acts for Curious People
- Creative DIY Microcontroller Projects with TinyGo...
- Cryptanalysis
- Crypto Trader
- Cryptography
- Culture Code
- Daniel Goleman Omnibus
- Deep and deliberate delegation
- Dhl
- Drive
- Effective Python
- Every Tool's a Hammer
- Exam Ref AZ-900 Microsoft Azure Fundamentals
- Expert Scripting and Automation for SQL Server...
- Fifty Quick Ideas to Improve Your User Stories
- Fixing Your Scrum
- Fundamentals of ServiceNow Administration and...
- Future Leader
- Future of Violence - Robots and Germs, Hackers and...
- GCHQ Puzzle Book
- Getting Things Done
- Harvard Business Review manager's handbook
- Hooked
- How Google Works
- How to Take Smart Notes
- How to Win Friends and Influence People
- HTML and CSS
- I Think, Therefore I Am
- Itsm Value Streams : Transform Opportun
- JavaScript and jQuery
- Kill It with Fire
- Leaders Eat Last
- Leading change
- Leading Without Authority
- Lean Thinking
- LONDON'S UNDERGROUND.
- Managing Successful Projects Prince2
- Managing Successful Projects with PRINCE2
- Measure What Matters : OKRs
- Meteorology today
- Mindf*ck
- Modern Cryptanalysis
- Modernist cuisine at home
- Money Revolution
- Never Split the Difference
- New One Minute Manager
- Open Circuits
- Oversubscribed
- Permanent Record
- PHP 5 advanced
- Practical Docker with Python: Build, Release and...
- Practical electronics for inventors
- PRINCE2 for dummies
- Pro Python 3: Features and Tools for Professional...
- Pro SQL Server Always On Availability Groups
- Pro SQL Server on Linux: Including Container-Based...
- Professional Scrum Master Guide
- Project to Product
- Radical Simplicity
- Rules of People
- SAFe 5.0 Distilled
- Sapiens
- SEARCH INSIDE YOURSELF- TPB
- Secret Barrister
- Securing SQL Server: DBAs Defending the Database
- Site Reliability Engineering
- SQL Server 2017 Administration Inside Out
- Start with Why
- System Center Configuration Manager Current Branch...
- T-SQL Fundamentals
- Teach Yourself Electricity and Electronics,...
- Teach Yourself Setting Up a Small Business (Teach...
- Team Topologies
- The Art of Deception
- The art of invisibility
- The Chimp Paradox How Our Impulses And Emotions...
- The coaching habit
- The code book
- The Courage To Be Disliked
- The DevOps handbook
- The Epic Guide to Agile
- The Five Dysfunctions of a Team: A Leadership...
- The Go Programming Language
- The Golden Ratio
- The Introvert's Guide to the Workplace
- The Manager's Path
- The New Silk Roads: The Present and Future of the...
- The outward mindset
- The Phoenix Project
- The Professional Product Owner
- The Unicorn Project
- Turn The Ship Around!
- Visual Thinking
- Weapons of Math Destruction
- Who Moved My Cheese?
- Work Rules!
- Working Out Loud
- Writing An Interpreter In Go
- Wrong Fit, Right Fit
Shared File Storage (Part 2): Knowing Your Audience
Previously, Shared File Storage (Part 1): Identifying Technical Debt discussed the importance of identifying technical debt.
In part 2 of this series, we explore the importance of understanding your audience. The term audience is used here to describe the people accessing the storage, their role and participation in the business, and the groups that are configured in Active Directory.
Groups are the key to keeping your NTFS permissions simple to manage, so identifying your different audiences and adding them to a set of standardised groups is the first step.
If you don’t already manage your departmental groups with an automated process, doing so will make lots of other processes simpler too.
The names of your groups should be predictable and easy to understand, especially in order to make use of automation and scripts to manage your groups and storage. It will also help with ambiguity and accidental reuse of a group beyond its original intention.
Unstructured group names increases the technical debt and the resources it takes to manage the NTFS permissions, whilst decreasing the accuracy of those actions.
In this example, we will use the following groups to define our audiences. There is a group for each definable group of people in the business.
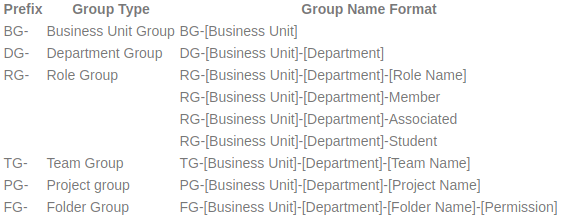
At first this may look like a lot of groups, and a lot to manage, but it’s not. Every member of the business will be associated with a business unit, department, role, team, or project.
The group membership should be nested for business units and departments, so a role group will be a member of the department, and the department will be a member of the business unit. Business units can be named after academic schools, colleges, professional services, or any other business unit names.
The folder group names should be suffixed with the level of access provided by the group, for example, full control, modify, or read-only.
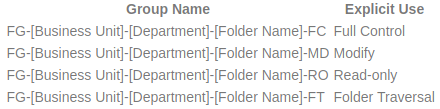
(Traverse folder / execute data,List folder / read data,Read attributes,Read extended attributes,Read permissions) The next part of this series will discuss how these audience groups translate into NTFS permissions.