- A Mind for Numbers
- Accelerate
- Agile Project Management for Dummies
- Algorithms to Live By
- Atomic Habits
- AWS Certified Cloud Practitioner Study Guide
- Banking on It
- Brexitland
- Build Your Dream Network
- Bulletproof SSL and TLS
- Business Analysis
- Collapse
- CompTIA Security+ Practice Tests
- CompTIA Security+ Study Guide
- Corporate Rebels
- Countdown to Zero Day
- Creative Acts for Curious People
- Creative DIY Microcontroller Projects with TinyGo...
- Cryptanalysis
- Crypto Trader
- Cryptography
- Culture Code
- Daniel Goleman Omnibus
- Deep and deliberate delegation
- Dhl
- Drive
- Effective Python
- Every Tool's a Hammer
- Exam Ref AZ-900 Microsoft Azure Fundamentals
- Expert Scripting and Automation for SQL Server...
- Fifty Quick Ideas to Improve Your User Stories
- Fixing Your Scrum
- Fundamentals of ServiceNow Administration and...
- Future Leader
- Future of Violence - Robots and Germs, Hackers and...
- GCHQ Puzzle Book
- Getting Things Done
- Harvard Business Review manager's handbook
- Hooked
- How Google Works
- How to Take Smart Notes
- How to Win Friends and Influence People
- HTML and CSS
- I Think, Therefore I Am
- Itsm Value Streams : Transform Opportun
- JavaScript and jQuery
- Kill It with Fire
- Leaders Eat Last
- Leading change
- Leading Without Authority
- Lean Thinking
- LONDON'S UNDERGROUND.
- Managing Successful Projects Prince2
- Managing Successful Projects with PRINCE2
- Measure What Matters : OKRs
- Meteorology today
- Mindf*ck
- Modern Cryptanalysis
- Modernist cuisine at home
- Money Revolution
- Never Split the Difference
- New One Minute Manager
- Open Circuits
- Oversubscribed
- Permanent Record
- PHP 5 advanced
- Practical Docker with Python: Build, Release and...
- Practical electronics for inventors
- PRINCE2 for dummies
- Pro Python 3: Features and Tools for Professional...
- Pro SQL Server Always On Availability Groups
- Pro SQL Server on Linux: Including Container-Based...
- Professional Scrum Master Guide
- Project to Product
- Radical Simplicity
- Rules of People
- SAFe 5.0 Distilled
- Sapiens
- SEARCH INSIDE YOURSELF- TPB
- Secret Barrister
- Securing SQL Server: DBAs Defending the Database
- Site Reliability Engineering
- SQL Server 2017 Administration Inside Out
- Start with Why
- System Center Configuration Manager Current Branch...
- T-SQL Fundamentals
- Teach Yourself Electricity and Electronics,...
- Teach Yourself Setting Up a Small Business (Teach...
- Team Topologies
- The Art of Deception
- The art of invisibility
- The Chimp Paradox How Our Impulses And Emotions...
- The coaching habit
- The code book
- The Courage To Be Disliked
- The DevOps handbook
- The Epic Guide to Agile
- The Five Dysfunctions of a Team: A Leadership...
- The Go Programming Language
- The Golden Ratio
- The Introvert's Guide to the Workplace
- The Manager's Path
- The New Silk Roads: The Present and Future of the...
- The outward mindset
- The Phoenix Project
- The Professional Product Owner
- The Unicorn Project
- Turn The Ship Around!
- Visual Thinking
- Weapons of Math Destruction
- Who Moved My Cheese?
- Work Rules!
- Working Out Loud
- Writing An Interpreter In Go
- Wrong Fit, Right Fit
Posts
Secure Your Home Lab With Lets Encrypt SSL Certificates, Caddy and Mythic Beasts DNS
A Home Lab is a valuable asset for any Developer or Engineer to support their personal development, personal projects, and experimentation. Web security is relentlessly improving, so we need to adapt our ways of working in order to support this. The days of running Production websites over plaintext http are long gone, and therefore we should also reflect this in our Home Labs too. There are many different ways to create a professional looking and secure Home Lab.
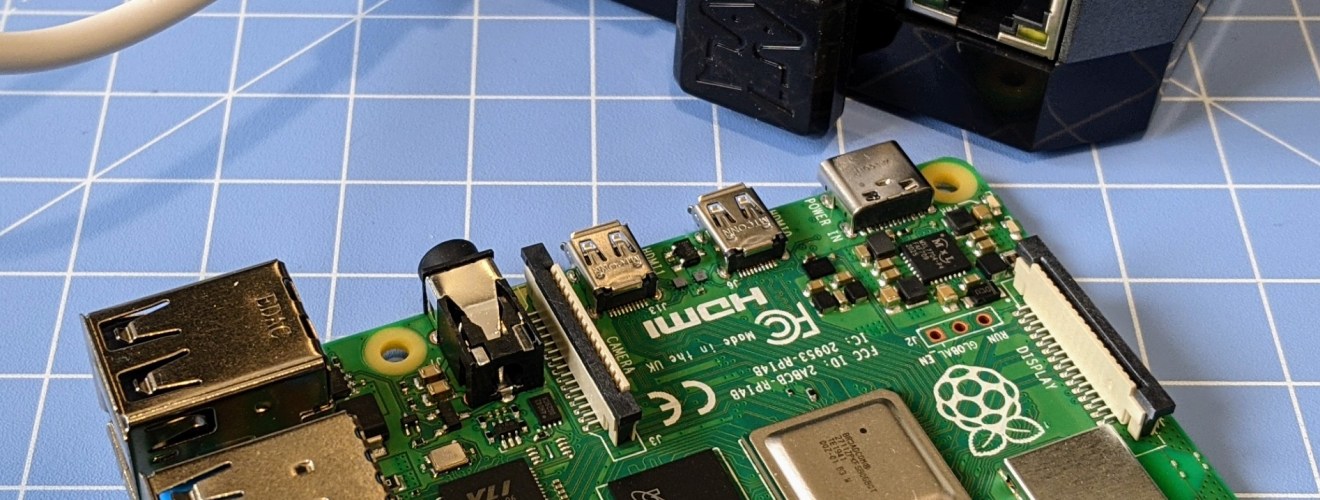
Installing OmniFeather with Feathercoin Wallet on a Raspberry Pi
Feathercoin is one of the oldest cryptocurrencies and has a thriving community. It is actively being developed with new and modern features that allows it to compete with other coins like Bitcoin. Transactions are quickly confirmed, and it is safe and secure. If you are interested in helping the network through mining, Feathercoin is suited to hobbyist mining with reasonably fast graphics card. The Feathercoin blockchain allows additional data to be stored within transactions, which can be used for things like token and contracts.

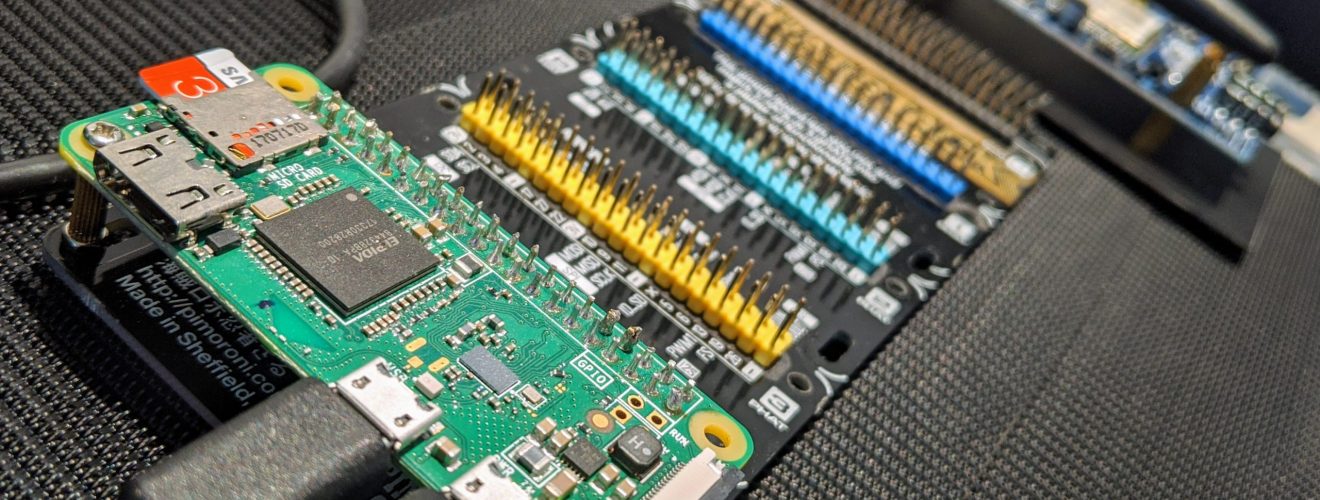
Learn about Satellites by building a Ground Station
Launching your own satellite into Space is becoming a relatively affordable option, but it still involves huge risk and costs. Whilst we won’t be launching our own satellites just yet, we can learn more about amateur satellites through educational and research projects. Participating in an existing project is easier than you may think, with a general understanding of computers, at the cost of a couple of coffees. It’s an impressive achievement when a project launches a satellite into Space, but it is arguably a more challenging achievement to build and maintain a global network of listening stations that make experimentation and observations possible.
Thinking inside the box – Introducing ChIoT
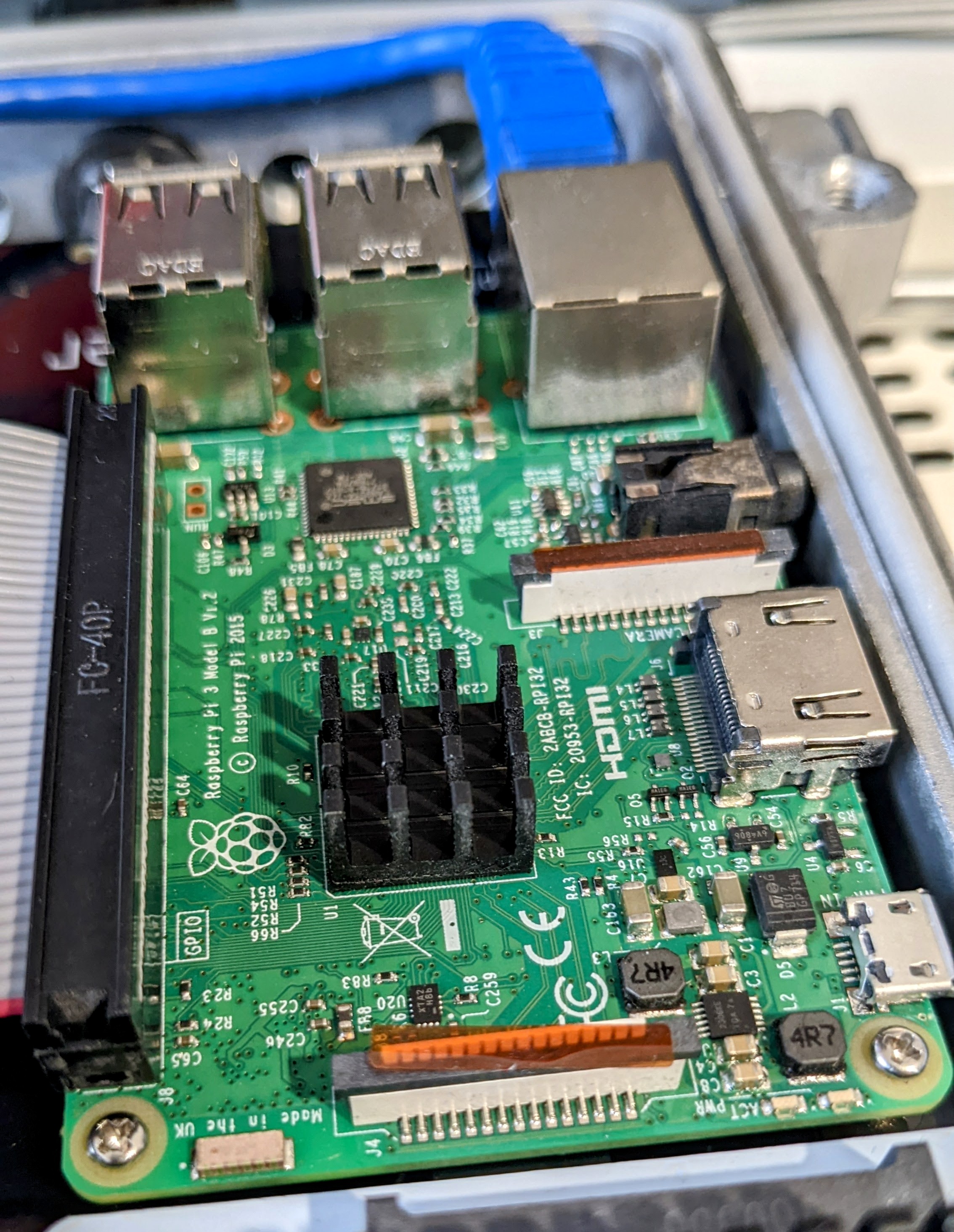
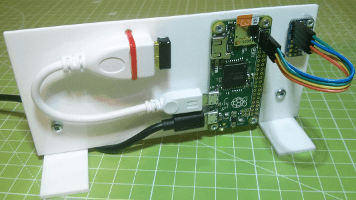
For a while now, I’ve been working on an Internet of Things (IoT) project that brings multiple ideas and learning objectives together into one well defined goal. The project consists of programming in Go (GoLang) and Python, writing modules for the production ready Caddy Server v2, using Raspberry Pi computers and other microcontrollers, and wiring up an endless supply of electronics. I have been creating Raspberry Pi stacks and development environments for years, but I always encounter the same problem.

Cross-skilling, Tooling, and Lockdown Bread
As I knead the dough in front of me, I realise two things. Firstly, I probably haven’t had enough exercise during Lockdown as this dough is beating me. Secondly, the automatic process of kneading allows for a clear mind in order to think. I’m almost finishing the sixteen kilogram bag of bread flour I purchased as lockdown began. This was bought through a local supplier which I knew it would only arrive when it was practical and sustainable.
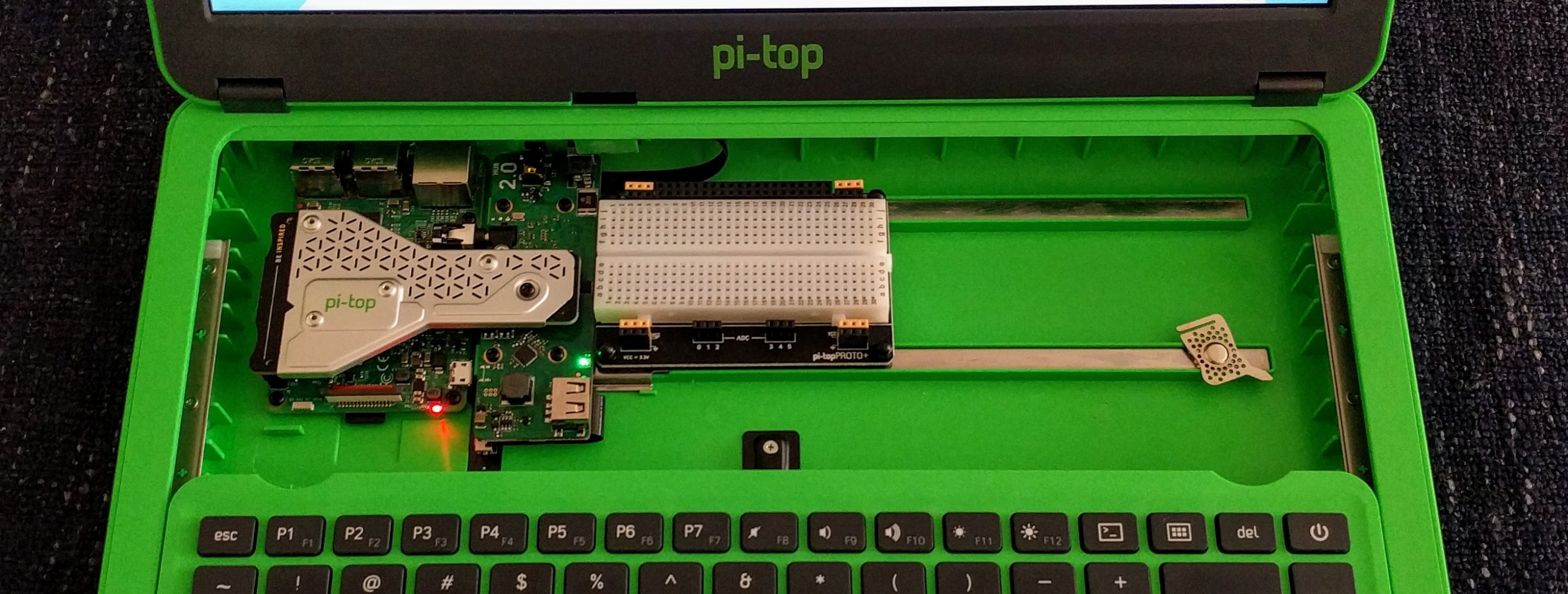
Learning with a Raspberry Pi powered Pi-Top laptop
Education and learning have always been important factors in my life. I have been using Raspberry Pi computers for many years as a tool for learning about the Internet of Things (IoT), programming, networking, and electronics. The pi-top laptop is designed for schools to teach computing, programming, and electronics. The new pi-top v2 has recently been released and I was interested in trying it out. I am programming in Go (GoLang) and reading from sensors connected to a Raspberry Pi, so it also makes sense to develop this code on a Raspberry Pi itself.

My Journey Through Education and Academia
“Mike Rother says that it almost doesn’t matter what you improve, as long as you’re improving something. Why? Because if you are not improving, entropy guarantees that you are actually getting worse…” — The Phoenix Project: A Novel About IT, DevOps, and Helping Your Business Win I have always loved computers. From the moment I owned my first ZX Spectrum, I have been on a mission to learn more. Like most children, my journey through education started in Play School, or more accurately for me, a big double decker Play Bus.

Using Gammu-smsd and MySQL to Send and Receive SMS Text Messages
In the previous post, Send and Receive SMS Text Messages with Raspberry Pi and SIM800 GSM Board, we connected up an Itead Raspberry Pi GSM Board (SIM800) from ModMyPi and configured Gammu to send and receive SMS text messages from the command line. In this post, we will install and configure Gammu-smsd to provide a MySQL database interface. This allows for more control and easier access to send and receive SMS text messages on your Raspberry Pi.
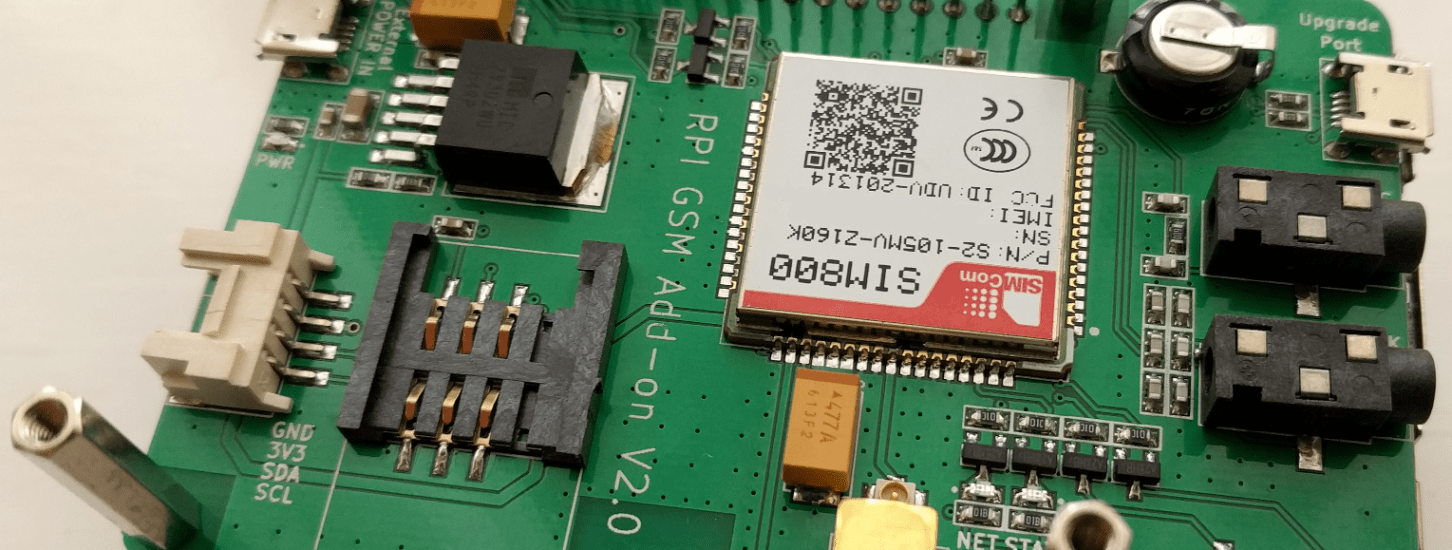
Send and Receive SMS Text Messages with Raspberry Pi and SIM800 GSM Board
The idea was a simple one. Connect up a GSM modem to a Raspberry Pi to send and receive SMS text messages. The ability to read SMS messages using serial AT commands is no longer possible with modern USB Mobile Broadband dongles, as some devices store their inbox beyond the reach of AT commands. After several days of tinkering with a low cost Huawei E3531, I finally gave up. There may have been other alternative methods to access the SMS inbox, but all these felt more like a hack than a solution.
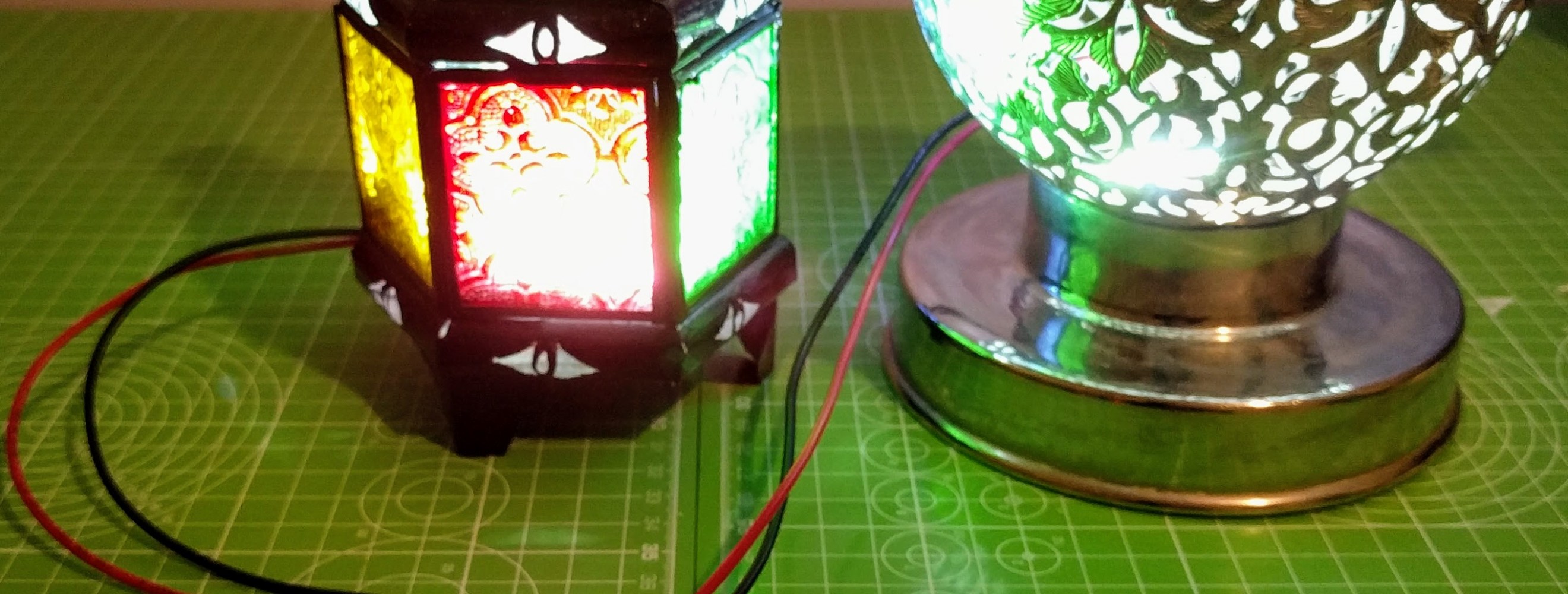
Raspberry Pi Controlled Lights Using Relays
We’ve had USB powered lights in our lounge for several years and every year I seem to slightly improve the wiring and relay boards. The Raspberry Pi below controls the lights behind our TV and are switched on using a Google AIY Voice Kit on another Pi mounted under our coffee table. (Voice Kit available here) It’s this Raspberry Pi that I am adding two more lights to. These new lights were purchased in the Souks in Marrakech and look great when lit up inside.
Monitor your heating using a Raspberry Pi and an MCP9808
During the winter season, we spend a lot of money heating our homes. Many heating systems are controlled by a basic thermostat installed in a random part of the home. It’s great to know whether the heating came on once, twice, or three times during the day. If the thermostat has been played with, it could have been on for longer than you require. I have been monitoring our heating system for several years and this year I decided to improve the wiring.

Understanding Higher Education for a University IT Job Interview
A reaction of surprise is often received from people when they realise you work at a university, rather than a student studying there. Working at a university is an inspiring and rewarding opportunity to be able to help thousands of students follow their dreams, study, research, and grow. After sixteen years in five universities, Higher Education is second nature to me. I really enjoy working in IT, and like most jobs, it’s the people that you work with and the people you support that make the job enjoyable.

Collecting Temperature Data with Raspberry Pi Computers
For several years, the temperature in our home has been monitored using Raspberry Pi computers. It’s interesting to see which rooms warm up the quickest and which rooms maintain their warmth longest, but that’s not the main reason that I originally setup the monitoring. The original reason for this monitoring was to improve my programming in Go (GoLang), writing network services, and designing APIs. Whilst designing, writing, and testing it is useful to have some test data that is randomly generated with minimal effort.

Locally mounting a Raspberry Pi Raspbian Linux image
It’s sometimes necessary to mount a Raspberry Pi Raspbian Linux image file before writing it to a SD card. This may be to configure an IP address, wireless settings, changing of passwords, etc. If you are using your Raspberry Pis headless without a screen, this can be helpful for the first time startup. Read more on configuring settings on Raspbian Linux images before writing them. This script may help with mounting a Raspbian image without having to do any calculations of where the partition start and finish.

Streaming TV using RTL-SDR and Raspberry Pi
I recently purchased several RTL-SDR DVB-T USB TV tuners from Pimoroni (DVB-T Dongle ideal for ADS-B). These USB devices are not just a great TV tuner, they are also a wide range software defined radio receiver. The supplied aerial is likely to be insufficient (which is fair enough considering the cost) so you will need a male MCX adaptor for your external aerial. The one I purchased from Amazon UK allows me to connect up my 2m 144MHz Amateur Radio aerial as I am looking to use the dongles for other purposes.

IoT – Preparing the Home for Autumn
The feeling of autumn is once again here, along with the desire to prepare for the coming dark nights and turning on the heating. During the summer, our collection of Raspberry Pi computers have been tasked with other purposes, but it is time to start recording the temperature again. Last autumn and winter, we experimented with using the MicroChip MCP9808 temperature sensors and Raspberry Pi computers to continiously record the temperature of each room in our home and to monitor the heating system to ensure it was running efficiently and being cost effective.

Ucisa Support Services Conference 2016 – Learning and Listening
This was my second year attending the Ucisa Support Services Conference. I shared my experiences from last year which described my first encounter of a conference of this kind, and some rules that made up a personal survival guide. This year I am writing about the listening and sharing of ideas. All Universities are tackling similar issues, and the SSG Conference is a great way to gather ideas and provide some perspective to compare your own journey.

Limitless Capacity for Data Storage in the Universe?
“If you think we’ve seen massive technology advances in the last 10 years, the next 10 will be like 1,000 years” — Jason Bradbury. At a recent lecture, The Gadget Show’s Jason Bradbury presented his prediction that the same amount of human progress made during the past 1,000 years, could be witnessed again within the next 10 years. Our advancement in technology is increasing at an exponential rate, as new technology makes the next round of technological advances possible.
Linux settings for Yubico FIDO U2F Security Key
Add the following lines to a new file called 70-u2f.rules, using the command nano /etc/udev/rules.d/70-u2f.rules ACTION!="add|change", GOTO="u2f_end" KERNEL=="hidraw*", SUBSYSTEM=="hidraw", ATTRS{idVendor}=="1050", ATTRS{idProduct}=="0113|0114|0115|0116|0120|0402|0403|0406|0407|0410", TAG+="uaccess" LABEL="u2f_end"
Modifying a Raspberry Pi Raspbian Image on Linux
If you have lots of Raspberry Pi computers, it’s useful to have an image that is preconfigured with your WiFi connections details, default password, default IP address, etc. I started by downloading the latest Raspian image from the Raspberry Pi Foundation Website. I am using the smaller Lite version, but will work for the full desktop image as well. After downloading the Raspbian image, ensure the checksum of the file matches the associated sha1 checksum from the downloads page.

Living Life in RAM – The Importance of Documentation
Imagine for a moment that your computer has no local storage and that everything running on it is saved into volatile system memory. Remove the power or reboot, and everything will be lost forever. The human mind is far more resilient, has less programming bugs, and more control over its actions and environment than a standard computer. But our human memories are stored in a similar way, and lost forever when the supply of energy runs out.
Learning about IoT and GoLang using MicroChip MCP9808 Temperature Sensors
Since the summer of 2015, I have been learning about the Internet of Things (IoT) with Raspberry Pi computers. IoT devices are the next generation of Internet connected devices that will soon fill our homes, from smart toasters and coffee tables, to smart fridges and freezers. I started out learning about Docker and Kubernetes, which I believe will be a future platform for running software on edge compute devices. It’s great that this technology scales down perfectly for low powered devices, but also scales up for clusters containing thousands of nodes.
Identity Management Systems: Using Multiple LDAP Directory Services
As an IT Professional with over fifteen years of technical experience and specialising in Identity Management, I have been involved with designing, supporting, and debugging identity management systems in several academic institutions. Identity management is present in every IT environment. It determines whether a user can log in, who they are, and what they can do. Even though identity plays such a crucial role in IT, it is often neglected, understood by only one or two people, or thought of in overly simplified terms compared to the actual complicated business logic and user lifecycle processes involved.
Shared File Storage (Part 2): Knowing Your Audience
Previously, Shared File Storage (Part 1): Identifying Technical Debt discussed the importance of identifying technical debt. In part 2 of this series, we explore the importance of understanding your audience. The term audience is used here to describe the people accessing the storage, their role and participation in the business, and the groups that are configured in Active Directory. Groups are the key to keeping your NTFS permissions simple to manage, so identifying your different audiences and adding them to a set of standardised groups is the first step.
Shared File Storage (Part 1): Identifying Technical Debt
I would like to share some ideas on designing an elegant structure for shared file storage. It is something that every organisation in academia has to design, tame, reorganise, redesign, and continually manage. Even in the cloud era, most of us won’t be saying goodbye to our fast, local, and reliable on-campus Windows shared storage. These thoughts on shared storage are my own and have been shaped by 15 years of experience in academic and business IT environments dealing with storage and identity management.
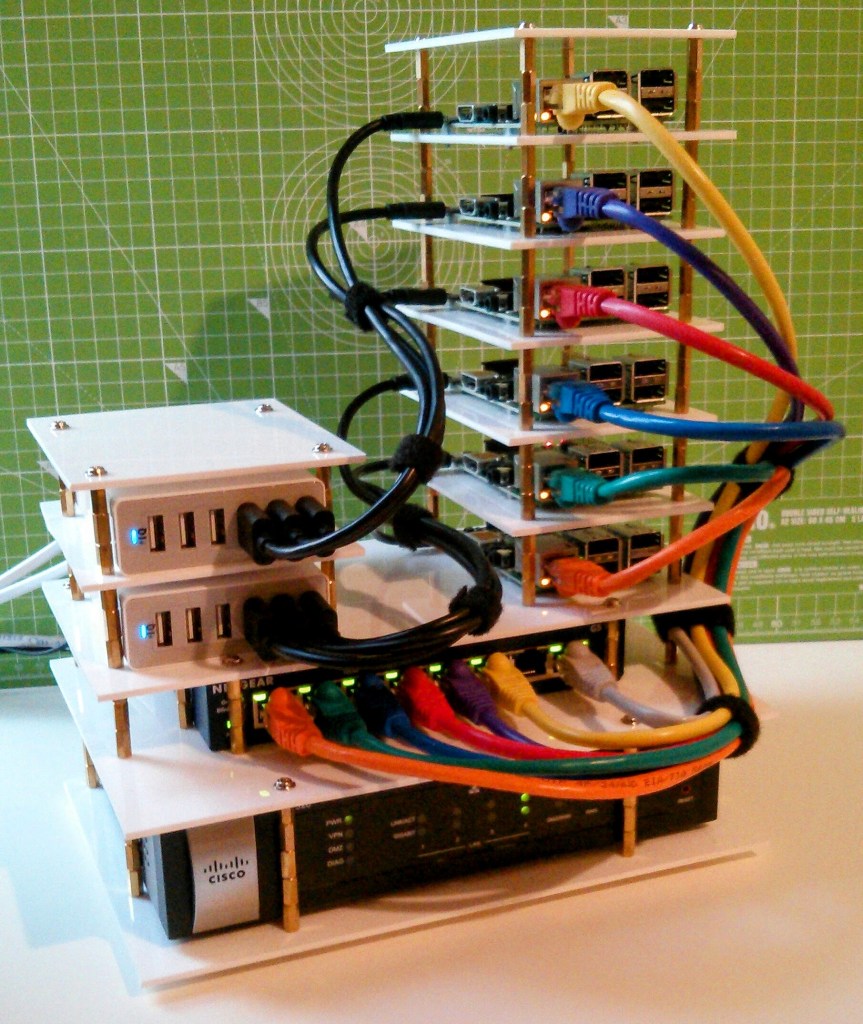
Raspberry Pi Stack – A platform for learning about IoT
During the summer of 2015, I decided to focus on learning about the ‘Internet of Things‘ (IoT) and the supporting technology. The Internet of Things will consist of lots and lots of low powered devices embedded in common household appliances and gadgets. The area that interests me most is the communications between IoT devices and the Internet, including the APIs, encryption, protocols, and algorithms that will make IoT possible. The programming language I am planning to use is called Go (GoLang).
A different way of thinking: Agile and Focused on IoT
Over the years, many people have been surprised that I enjoy IT outside of work, as much as I do in work. During those years, my inquisitive mind has asked and answered many questions. Its mainly been a series of little experiments and learning along the way. Whilst this is really interesting and rewarding, it doesn’t really give you any constructive output. Instead of a bouncing between a set of experiences, I’ve decided to focus on a specific area, and its supporting technology.
Powershell: Recursively List Folder NTFS Access Control Lists
This script will recursively list the NTFS Access Control Lists on folders in a large folder structure. It outputs the non-inherited ACLs on each folder recursively and shows where inheritance has been disabled. The NTFSSecurity module supports path lengths up to 32,768 characters. The output formatting could do with some improvement. In the future, I am looking to dump this data into a database, instead of the console. PowerShell Version: 4 Required PowerShell Module: NTFSSecurity Further Reading: Weekend Scripter: Use PowerShell to Get, Add, and Remove NTFS Permissions [CmdletBinding()] Param( [Parameter(Mandatory=$True,Position=1)] [string]$path ) Import-Module NTFSSecurity function ProcessChildren ([string]$path) { $children = Get-ChildItem2 $path -Directory foreach ($child in $children) { ProcessChild $child.
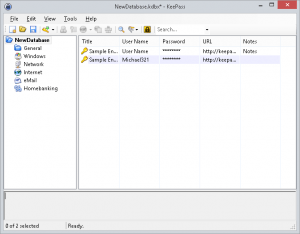
Improve your password security with KeePass 2 x
Would you continue to use your toothbrush after using it to clean the toilet? Obviously not, but often we like to reuse passwords for multiple websites and services. It’s not easy to remember great passwords for every website, so we need a secure method of storing them. The reusing of passwords is dangerous, and these days we regularly hear of websites that have been hacked and the user information has been made available on the Internet for fraudsters and hackers to abuse.
Ucisa Support Services Conference 2015 – The Experience
Recently, I attended the Ucisa Support Services Conference 2015. This was my first Ucisa event. It was great to network with Service Desk Managers, Customer Service Managers, IT Directors, organisers, and event sponsors. The theme was ‘Change is the only constant’. I knew that getting the most out of these events is dependant on what you put into them, so I was prepared to start networking. The more you network and get involved, the greater the experience and overall achievement.